In a recent post (https://enterpriseadmins.org/blog/virtualization/domain-controllers-and-micro-segmentation/) I described an issue where authentication may not work as desired when Active Directory sites and Services Subnets are not properly defined. There is often a disconnect in large enterprises where network/subnet creation and active directory aren’t managed by the same folks, so occurrences like the one I described are all too common. I remember many years ago writing a VBScript that parsed a log file to try and find new networks so that we could create subnet definitions. I decided to see what new options existed in this space and was surprised to see that things were mostly unchanged.
Active Directory authentications from clients without subnets defined are still logged to C:\WINDOWS\Debug\netlogon.log all these years later. This file contains entries such as:
05/12 21:28:11 [6772] LAB: NO_CLIENT_SITE: EUC-VIEWCS-21 192.168.36.50
This suggests that the subnet I use for VDI Management VMs is not mapped to a site in AD Sites and Services through a properly defined subnet. In this case I know that the network 192.168.36.0/24 should map to my US-East-IN site in Active Directory. This is an easy fix, but in dynamic environments something similar is going to happen again.
The old VBScript would still work to parse this file, and I could run that as a scheduled task, and occasionally look for these types of events. However, thanks to vRealize Log Insight, I have better ways to deal with log files in my lab these days. All of the systems deployed in my lab run the Log Insight agent, which can be used to pickup this file. I already have a custom Agent Group for my domain controllers, so I can just edit its configuration so that it also picks up the file. To do this, I browse to Management > Agents > select the group “Domain Controllers” > File Logs > New and create an entry for the path in question:
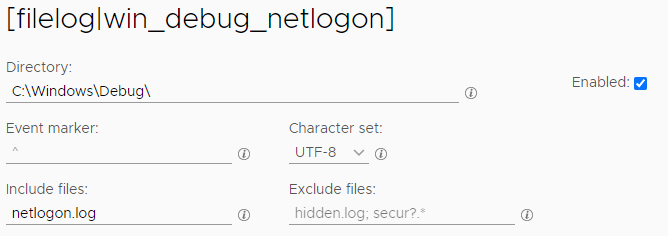
As you can see, we are looking in the C:\Windows\Debug\ directory, specifically for one file named netlogon.log. After adding this entry I selected ‘Save Agent Group’. After a couple of minutes I searched Interactive Logs for no_client_site and had a few hits. This works well, but what I really want to see is which clients are showing up without needing to parse through all of these individual rows. To help with this I can make a custom dashboard based off an extracted field.
Extracted Field
I can see that the data I want is right there at the end of the string, so I can highlight the text and click ‘Extract field’. This brings up a ‘Manage Fields’ screen in the right navigation. By default, the wizard knows that I want to extract an IP Address, but it thinks I only want the one that comes after a specific hostname:

I can simply change this from EUC\-VIEWCS\-21 to (a single space) and it automatically highlights all the entries, not just this one. I can name the field and select save.
Custom Dashboard
From the explore logs view, I queried for no_client_site I changed the dashboard selections at the top to ‘Count of events’ and grouped by ‘WinDebug_NoClientSite_IP’ which is the name of the extracted field from above. This resulted in a bar graph by the authenticating client where I could easily see the handful of interesting clients.
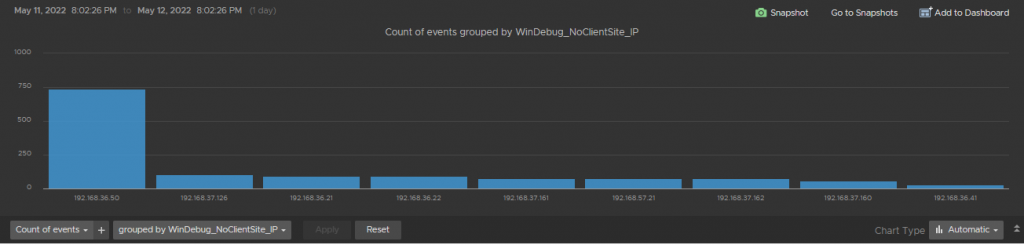
In the top right of this visual is an ‘Add to Dashboard’ button. I used that button to add this newly created chart to a ‘Active Directory – Custom’ dashboard that I have started.
I now have a visual that will show me the clients that are in subnets not mapped to an Active Directory site. Once I research these subnets and get them properly defined this query should return no results — until the next time a network is created.

Pingback: vExpert Cloud Management May 2022 Blog Digest - Möbius Business Technologies Ltd.